My Private key was compromised.
This is where I originally posted all my research & investment thesis:
Hence, I’m re-uploading all my writings to this account.
Please subscribe to this new account and support me in my research.
This research was originally posted on April 18, 2023.
Despite being only three weeks into Q2, we've already witnessed a string of hacks and exploits targeting various defi protocols and DEXs.
But fear not, as I've thoroughly researched and analyzed a few of these incidents to provide insights into how they happened and what can be learned from them.
(April 13, 2023) Yearn Finance & AAVE were exploited for more than $10M.
yUSDT token, which is supposed to be a yield-generating version of USDT, was misconfigured to use Fulcrum's iUSDC token instead of iUSDC and stayed that way for more than 1000 days.

This situation leads to unexpected (losses or gains) for anyone holding yUSDT, depending on the exchange rate b/w USDT and USDC.
Understand what this is in detail:
-
Fulcrum is a margin lending and trading platform that uses tokenized loans (iTokens) & tokenized positions (pTokens) that use algorithmic lending pools to determine interest rates through supply and demand.
-
iTokens are interest-bearing tokens representing a share of Fulcrum's lending pool. Users can deposit their crypto assets into the pool and receive iTokens in return, which accrue interest over time.
-
iUSDC and iUSDT are two types of iTokens based on USDC and USDT, respectively.
-
The yUSDT token is supposed to be a yield-generating version of USDT, created by Yearn Finance, that allows users to earn interest on their crypto by depositing them into various pools or vaults.
-
However, it was discovered that the yUSDT token was misconfigured to use the iUSDC token instead of the iUSDT token as its underlying asset.
This means that the yUSDT token was actually using a different stablecoin (USDC) than what it was supposed to use (USDT)
According to lookonchain,
-
3,032,142 $DAI
-
2,579,483 $USDC
-
1,785,091 $BUSD
-
1,512,528 $TUSD
-
1,193,756 $USDT
were exploited.
OtterSec explained in detail how the exploit took place:
The hack was initially discovered by Samczun here:
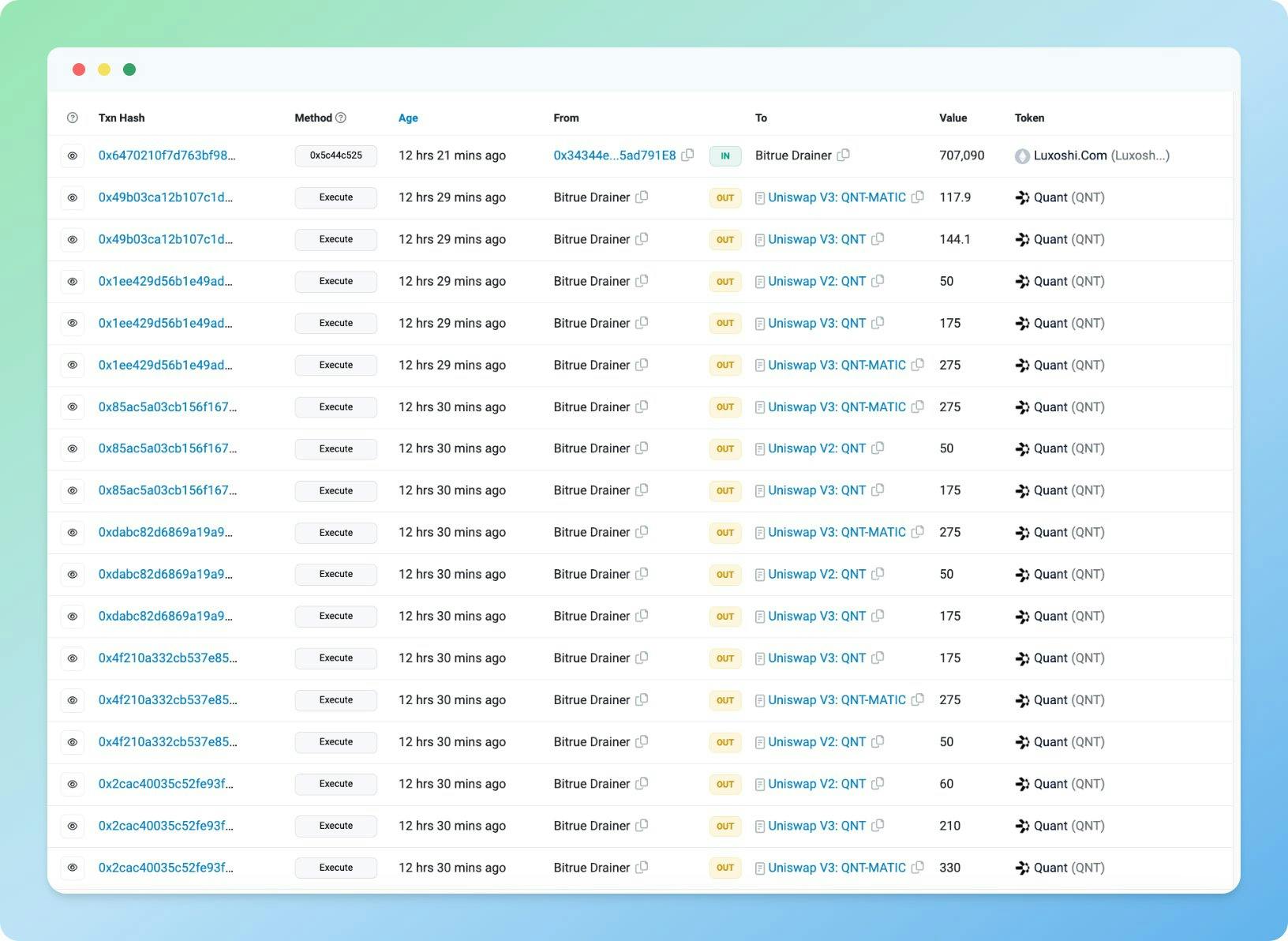
(April 14, 2023) Bitrue Exchange was Exploited for $24M
Bitrue crypto exchange suffered a hot wallet exploit, losing nearly $24M in crypto assets. According to the exchange, the stolen tokens represented 5% of Bitrue’s overall funds.
Bitrue paused withdrawals after the hack and intends to reopen them on April 18.
Details below:
-
The hacker exploited the hot wallet by using an unauthorized transaction involving $ETH & $USDT.
-
Bitrue does not disclose the exact details of how the hacker accessed the hot wallet.
Still, it is possible that they exploited a vulnerability in either
-
the hot wallet software or
-
used a phishing attack to obtain private keys or credentials.
The hacker managed to withdraw various tokens worth nearly $24M, including BTC, XRP, ADA, QNT, GALA, SHIB, HOT & MATIC.
The hacker used multiple external addresses to withdraw tokens from Bitrue’s hot wallet and exchanged most of these tokens for 8,858 $ETH, currently in a wallet with the address 0x181. They did this to avoid being traced and to exchange the tokens for other cryptocurrencies.
Why are hot wallets so prone to hacks?
Hot wallets store the private keys or credentials that allow users to access their funds on the exchange.
Hackers can withdraw funds from the hot wallet to external addresses if they obtain these keys or credentials. They can also exploit vulnerabilities in the hot wallet software or the exchange’s security system to access the hot wallet.
Hot wallets are usually used to store a small portion of the exchange’s total funds, while most are held in cold wallets, which are offline wallets used for storage.
However, some exchanges may store significant funds in hot wallets to facilitate liquidity and trading volume. This increases the risk of losing a substantial amount of funds in case of a hack.
(April 16, 2023) Hundred Finance was Exploited for More than $7 Million.
Hundred Finance was hacked by an attacker who exploited a vulnerability in the $hWBTC market on Optimism.

-
The attacker manipulated the price of hWBTC by depositing and withdrawing $WBTC to inflate the value of hWBTC relative to other assets.
-
The attacker then used the inflated $hWBTC as collateral to borrow funds from other markets on Hundred Finance, such as $ETH, $USDC, $DAI, etc.
-
The attacker could borrow more than the value of their collateral because of price manipulation.
-
The attacker then withdrew the borrowed funds from optimism to ethereum, leaving behind a large debt on Hundred Finance.
The total loss for the protocol was estimated at around $11M.
So why did this happen?
The hacker used a "re-entrancy" attack to exploit the protocols. A "re-entrancy attack" works by allowing the hacker to call the same function multiple times before the state of the contract is updated and thus borrow more funds than their collateral. (I have explained how this works step by step in the following tweet)
The hacker donated 200 WBTC to Hundred Finance, which gave them 200 hWBTC in return, then they deposited 500 WBTC, which increased the price of hWBTC by 250 times, then used hWBTC as collateral to borrow funds from other markets.
-
The hacker donated 200 $WBTC to Hundred Finance by calling the deposit function on the $hWBTC market contract with 200 WBTC as the input parameter.
-
The protocol gave them 200 $hWBTC in return for minting new $hWBTC tokens and sending them to the hacker’s address.
-
The hacker deposited 500 $WBTC, which increased the price of hWBTC by 250 times by calling the "deposit" function again on the hWBTC market contract with 500 $WBTC as the input parameter.
-
The price of hWBTC increased by 250 times because the protocol calculated the exchange rate of hWBTC based on the ratio of WBTC and hWBTC in the pool, meaning that after the hacker deposited 500 WBTC, there were more WBTC than hWBTC in the pool, so each hWBTC was worth more WBTC than before.
-
The hacker used hWBTC as collateral to borrow funds from other markets by calling the borrow function on different market contracts with their hWBTC as the input parameter, meaning that they used their inflated hWBTC tokens to take other tokens from the protocol, such as $ETH, $USDC, and $DAI.
The reasons why this happened were threefold:
-
Re-entrancy vulnerability in the $hWBTC market on Optimism, meaning that the attacker could call the same function multiple times before the state of the contract was updated.
-
Lack of price oracles for $hWBTC, meaning that the protocol relied on the internal exchange rate of hWBTC, which the attacker could easily manipulate.
-
Low liquidity of $hWBTC, meaning that the attacker only needed a small amount of $WBTC to inflate the price of hWBTC by a significant factor.
These reasons combined allowed the attacker to create a massive discrepancy between the value of their collateral and their debt and drain the funds from other markets.
How re-entrancy attacks work step-by-step:
-
The hacker finds a function in the contract that makes an external call to another contract and does not update the state before the call.
-
The hacker calls this function with their own malicious contract as the recipient of the external call.
-
The function checks if the hacker has enough collateral to borrow some funds from the contract and sends them the funds.
-
The malicious contract receives the funds and triggers its fallback function, which is a default function that runs when no other function is specified.
-
The fallback function calls the same function in the original contract again before the state is updated.
-
The function checks if the hacker has enough collateral to borrow some more funds from the contract and sends them more funds.
-
The malicious contract receives more funds and triggers its fallback function again, repeating the process until the original contract runs out of funds or gas.
-
The hacker ends up borrowing more funds than their collateral because the original contract never updated its state to reflect the previous withdrawals.
Also, Mudit Gupta mentioned here that Agave's smart contract was very similar to Aave's smart contract, but Aave’s had more safeguards to prevent re-entrancy attacks.
Some people in my network mentioned that the best way to prevent re-entrancy attacks from happening would be to:
-
make sure the contract updates its records before giving any money to anyone.
-
use some code that prevents the same function from being called again until it is done.
-
use a safer method of sending money that stops the function if something goes wrong.
(April 3, 2023) A Solo Validator Exploited Five MEV Bots and Earned a $20M Block reward.
Samczun found out about this
Simpler explanation of this:
Ethereum is a big playground where people can play games and trade toys. Some people have special machines that can make new toys and give them to others who play the games. These machines are called validators. Sometimes, people want to trade their toys with other people, but they have to pay some candy to the validators to make the trade happen. The more candy they pay, the faster the trade happens.
Some people are very smart and sneaky, and they try to trick other people who are trading their toys. They see what toys they want to trade and quickly offer a better deal to the person who has the toy they want. They also pay more candy to the validators to make their trade happen first. This way, they get the toy they want for a cheaper price, and then they can sell it for a higher price later. This is called front-running.
There is a group of people who want to stop this from happening. They are called Flashbots. They have a special network connecting them with the validators, and they let people send their trades directly to them without anyone else seeing them. They also let people pay extra candy to the validators if they want their trades to happen faster. This way, they can avoid being tricked by sneaky people.
However, Flashbots has a problem with its network. Sometimes, when people send their trades to the validators, they don’t send all the information about their trades. They only send a secret code that represents their trades. The validators must ask Flashbots for the rest of the information before making the trade happen. But sometimes, Flashbots can’t give them the information because of a mistake in their network. This makes the validators unhappy, and they can’t make the trade happen.
One person found out about this problem and decided to use it for their own benefit. They made a fake trade that looked like a real one, but it was actually a trick. They also made two other trades that would help them make more money from their fake trade. They put these three trades together and sent them to Flashbots with a secret code and a lot of candy for the validators. The validators saw the secret code and the candy and wanted to make the trade happen. But when they asked Flashbots for the rest of the information, Flashbots couldn’t give it to them because of their mistake.
The person then waited for a validator not using Flashbots’ network. They sent them all the information about their three trades and even more candy. The validator didn’t know that one of the trades was fake and a trick. They accepted all the information and made the trade happen. The person then made a lot of money from their trick and gave some of it to the validator as candy.
The person made about $20 million from this trick, which was paid as candy by Flashbots to the validator who made their trade happen. This was not a regular candy reward but a special candy reward from tricking other people who were trading their toys.
There’ll be many more, so be sure to subscribe so that you get these posts in your email directly.
Also, Let's not forget that early internet hacks were commonplace - from nerds hacking their school grades to stealing login info and creating viruses.
Impact on us?
It's no surprise that DeFi faces similar challenges, one we saw with YearnFinance & AAVE or Bitrue or Hundred Finance, but we're holding our own.
Thank you for reading through, and subscribe below for regular post updates.
I’d also appreciate it if you shared this with your friends, who would enjoy reading this.
You can contact me here: Twitter and LinkedIn.